Russian Cybersecurity Experts Aim to Put AI Back on the Defensive Side
As AI-driven attacks grow more sophisticated, cybersecurity firms are using the same technologies to build proactive, system-level defenses against fraud and cybercrime.
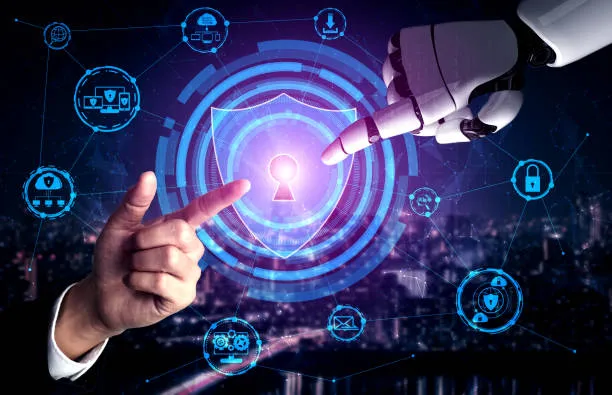
According to experts at Positive Technologies, artificial intelligence will become one of the main drivers of cyber threats in 2026. But AI is not only a tool for attackers. Cybersecurity specialists are increasingly turning it into a practical resource for defending businesses, using the same technologies employed in attacks to create more resilient security architectures.
Personalized Attacks at Scale
Analysts warn that the automation of cybercrime is dramatically lowering the barrier to entry. Even attackers with minimal technical skills will be able to carry out complex, highly personalized campaigns—generating phishing emails, tailoring social engineering to specific individuals, and deploying ready-made hacking tools.
Additional risks come from the growing use of public AI services by employees for work-related tasks, often without fully understanding the security implications. Analysts also point to a rise in attacks targeting the industrial sector. IT companies and service providers remain at risk as well, since their infrastructure is increasingly used as an intermediate entry point for attacks on partners and customers.
From Reactive Defense to Digital Hygiene
Against this backdrop, more organizations are abandoning reactive security models—where action is taken only after an incident—and shifting toward proactive defense strategies.
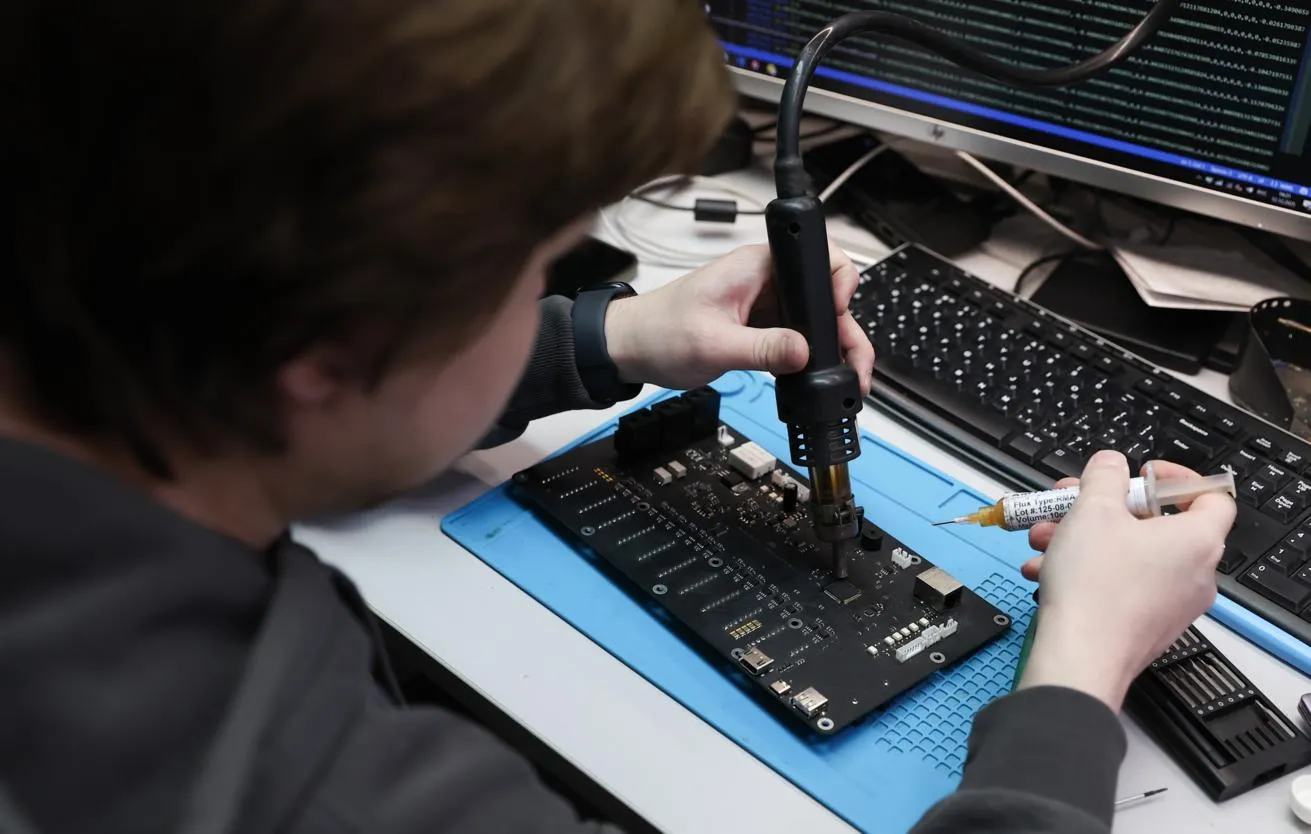
The company argues that real protection starts not with fashionable technologies but with basic infrastructure hygiene. This includes maintaining a complete inventory of digital assets, systematically managing vulnerabilities through VM platforms, monitoring network traffic, and filtering email and web-based threats. Increasing attention is also being paid to application security and employee training, including guidelines for safely using AI services.
To detect attacks and respond quickly, organizations deploy tools such as SIEM, NTA, EDR, and EPP solutions, subscribe to threat intelligence feeds, and participate in threat data–sharing platforms. These measures are complemented by cyber exercises and regular resilience testing, which help identify weaknesses before attackers can exploit them.
Experts agree on one point: in the new threat landscape, success belongs not to companies with the most individual tools, but to those that build coherent systems—combining continuous monitoring, trained personnel, and clear incident-response logic.
According to Positive Technologies, the systemic approach adopted by Russian cybersecurity specialists has already proven effective in practice. Critical infrastructure has avoided major systemic failures and demonstrated a high level of resilience under real-world conditions.